Many of us who are working with large or small implementation of office 365 might be using Password HASH Sync as authentication method or moving towards it to simplify the architecture.
I am sure many of us are already aware that PHS (Password HASH Sync) does not honor password expiry, account expiry or signin hours.
This means if user password is expired then also, he can login to o365 services or other services if Azure AD is the authentication provider.
We have shown that to some of our clients as well by logging in with expired password for as many days as we want, as in AzureAD it is set as never expire.
One of our clients is working with well known firm to move from on-premise federated solution to AzureAD with PHS.
After finding this they reached out first to their Vendor, but Vendor has not provided them any solution and told them it is what it is.
We have come up with a PowerShell solution which we have tested and will be scheduling it in their environment. (and sharing with the community)
Note: Microsoft is also working on it and they have few out of the box solution but it is still is not up to the mark.(not going in details about it)
For details refer:
password hash synchronization with Azure AD
Download the solution from below Github or install it from Powershell gallery:
https://www.powershellgallery.com/packages/FixPHSPasswordExpiry
Install-Script -Name FixPHSPasswordExpiry
https://github.com/VikasSukhija/Downloads/blob/master/FixPHSPasswordExpiry.ps1
Prerequisites:
- Msonline Module
- Azure AD module
- Active Directory Module (This is part of remote server administration tools or adminpak for client OS)
To run the Script, you can run it from PowerShell
.\FixPHSPasswordExpiry.ps1 -smtpserver smtpserver -from DoNotReply@labtest.com -erroremail Reportslogs@labtest.com -countofchanges 20 -logrecyclelimit 60
Smtpserver à Smtp server
From à from address from which email will be sent
Erroremail à email address on which log, or error will be sent.
Countofchanges à This has been built for protection so that if you see more changes than this number script stops and does not process anything.(optional default value is set as 20)
Logrecyclelimit à
This has been built to recycle the logs after number of days (optional default value is set as 60)
Logs are placed in logs folder and recycled after 60 days or based on your input in parameter.
Note: First time you have to provide the adminid and password to connect to AzureAD (it will save the password in encrypted form in the same folder so that you can schedule it)
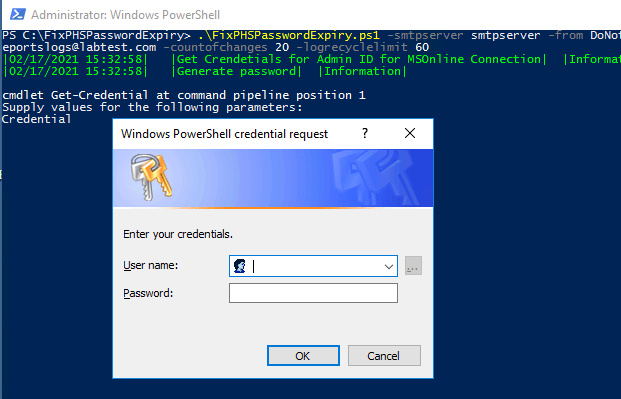
See below screenshot, it will start fetching enabled accounts with password expired set to true.
After fetching all accounts that are expired in onpremise AD, it will connect to AzureAD and check if force password change on next login is already set to true then do nothing else use msonline and set force change password flag.
Set-MsolUserPassword -UserPrincipalName $upn -ForceChangePassword:$true -ForceChangePasswordOnly:$true
Note: After first run you will not be asked for password again unless you delete the password.xml file.

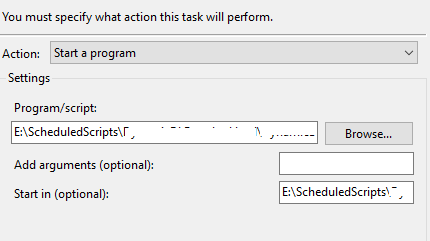
To schedule a script, you can create a batch file and add it in task scheduler.
Powershell .\FixPHSPasswordExpiry.ps1 -smtpserver smtpserver -from DoNotReply@labtest.com -erroremail Reportslogs@labtest.com -countofchanges 20 -logrecyclelimit 60
If you want a simple fix that runs daily, then this script will assist you in fixing the gap that arose due to PHS.
Thanks for reading and downloading….
Tech Wizard
Hi,
Is it possible to set this up to use office365 as the smtp using tls?
I was able to make this work using office365 as my mail server, thanks for this great script.