We have recently implemented Azure AD Privileged Identity Management for one of our client so just want to share some of the important points.
- Now no one is Global Admin, Exchange Admin, Sharepoint admin or in any admin role that is impactful.
- It is just plug and play to implement.(piece of cake)
- Azure AD P2 or EMS E5 or M5 license is required (each admin that is using PIM should have that license)
- Each admin can activate the role for certain hours and after that role gets auto deactivated.
- Approval facility is also there, in case you want that certain role require a approval before activation.
Limitation:
- You can not set the setting for a Role (for example: global admins) that certain people require approvals and others do not require it.
This granularity is not available as of now, one set of settings for each role is only available.
We have consulted this with Microsoft and this is on their Road Map so may be released next year.
Implementation:
First make sure you own appropriate licenses (Azure AD P2 or EMS E5 or M5) and it is assigned to your account.(assumption here is that you are doing this configuration from Global admin account)
Now log on to https://Portal.Azure.com and search for PIM
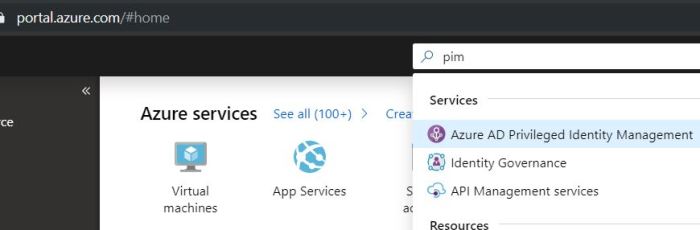
Select Azure AD privileged Identity management and provide your consent to activate it on your tenant.
It will verify your identity via MFA and than you will be able to activate it.
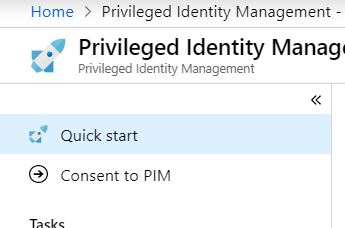
Ones activation is done you will be auto added to the Privileged Role Administrator, This role allows you to manage the PIM.
First go to Settings –> Roles
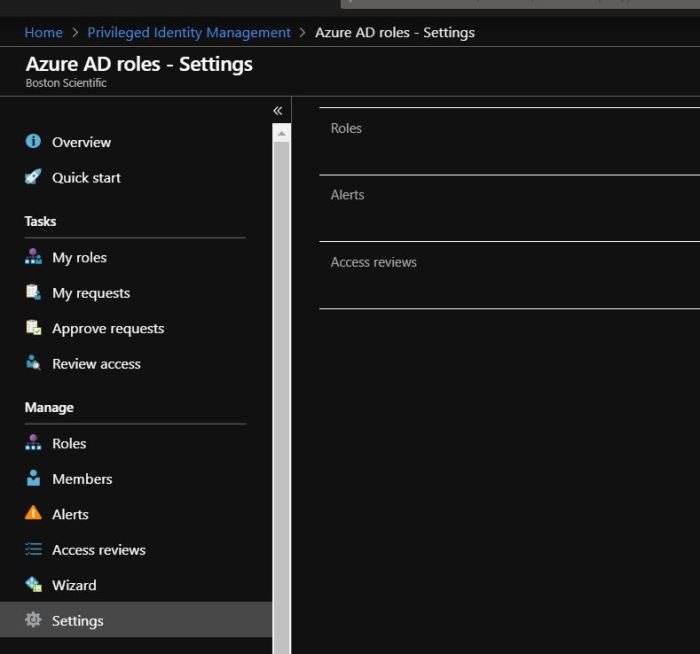
Select the role for which you want to enable PIM for example Global Administrator.(update the settings that you want for this role and save it)
Do not worry, nothing will happen to existing admins( They will remain permanent admins until we change later them to eligible)

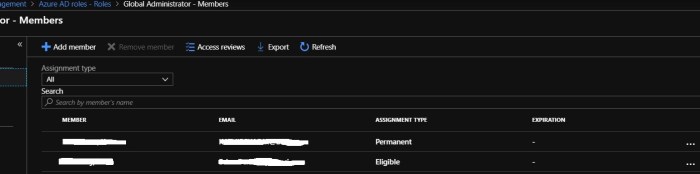
Now go back, click on roles and select Global administrator
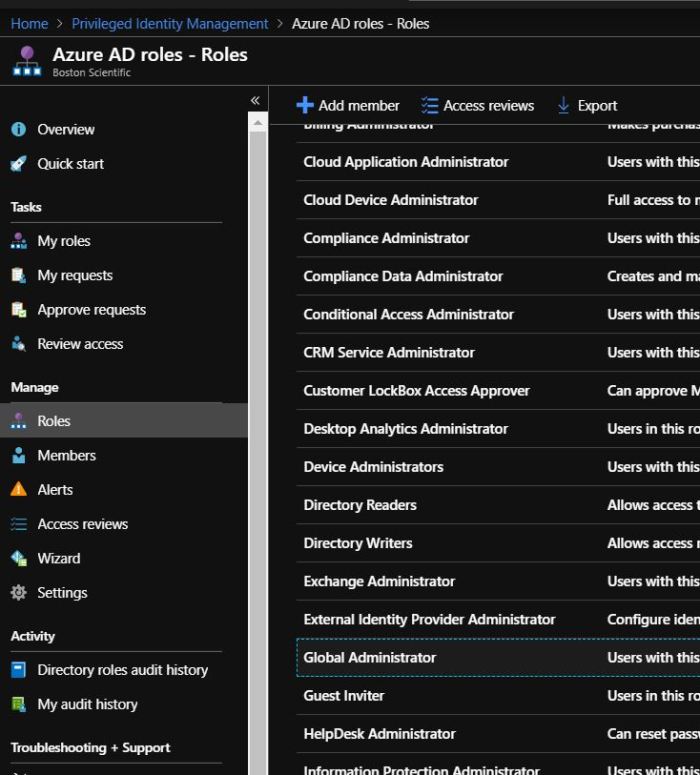
Select the Admins for whom you want to enable PIM, click on three dots (…) to make them eligible.
We have made everyone eligible except one of the service account (which acts as our back out account as well)
When above is completed, below are the steps that needs to be followed by Eligible admins to become Admin.
Admin will go to PIM portal on https://portal.azure.com
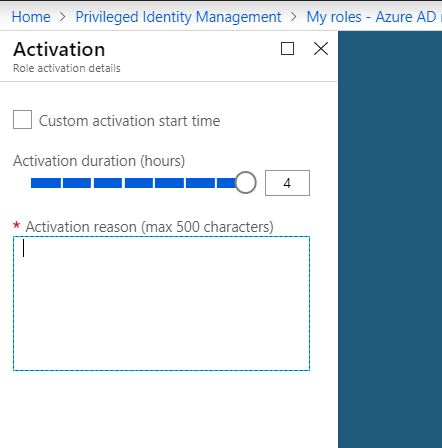
Click on my roles and select the role that you want to activate –> hit activate.

It will ask you to identify your identity(MFA comes in play here)
ones you have done the successful identification go back to PIM again and click on activate, select the number of hours, reason and it will activate.
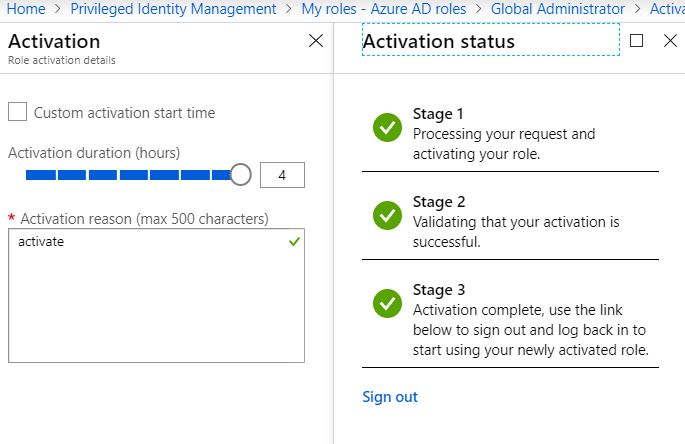
sign out, close browser and open again, you can now perform all global admin activities.
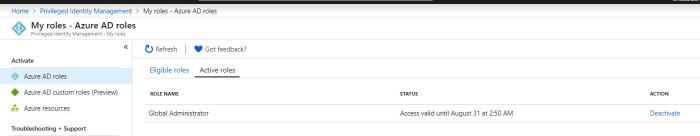
Role will auto deactivate after 4 hours, if you have finished the work early then you can deactivate the role yourself as well.
Go back to my roles in PIM , click on active roles and deactivate.
So you have seen how simple it is to implement PIM and it makes your environment secure as admin role is activated on requirement basis, also they have to identify themselves via mfa before activating the role.
Thanks for reading
Sukhija Vikas
Pingback: Extract Report – Azure AD Privileged Identity Management – Part 1 | Tech Wizard