Many organizations want to block automatic forwarding set by users, and we have to do multiple configurations on Exchange online to achieve this.
Here are the requirements:
-
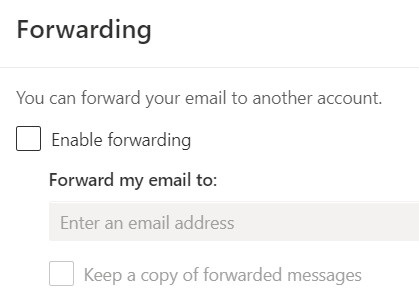
Block external forwarding set by users in OWA.
-
Block external forwarding set thru outlook rules.
-
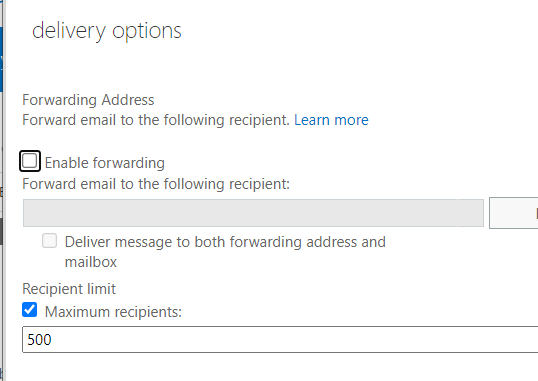
Block external forwarding set by exchange admins using exchange console or shell.
- Allow external forwarding for exception group of users.
- Allow external forwarding for Powerautomate
All this we must do without impacting existing forwarding rules set by users or admins as those users will be tackled later.
As a step number 1 we will target the first avenue that is OWA settings without impacting the existing users that have already used it.
You can achieve this by creating new RBAC and then activating it in the default role assignment policy for users.
By default, below is the policy:
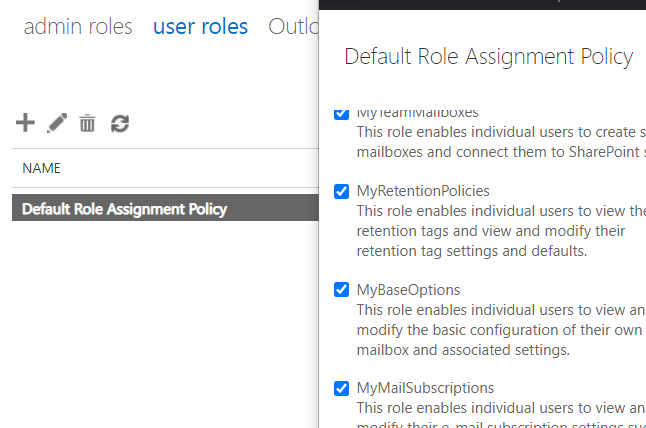
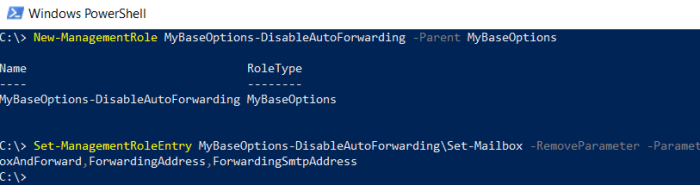
Use exchange management Shell and create new management Role
- New-ManagementRole MyBaseOptions-DisableAutoForwarding -Parent MyBaseOptions
- Set-ManagementRoleEntry MyBaseOptions-DisableAutoForwarding\Set-Mailbox -RemoveParameter -Parameters DeliverToMailboxAndForward,ForwardingAddress,ForwardingSmtpAddress
-
Verification by using (Get-ManagementRoleEntry MyBaseOptions-DisableAutoForwarding \Set-Mailbox).parameters
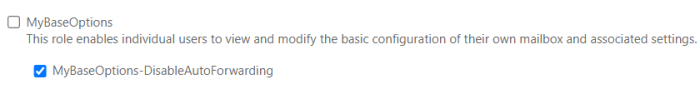
Now go to ECP and update the Default Role Assignment Policy, uncheck MyBaseOptions and Check MyBaseOptions-DisableAutoForwarding
Note: If you are exchange admin you will still see the forwarding option in OWA, but users will not see after above change for obvious reasons (your role has those assignments thru admin privileges)
Before doing below, we need to first get the report so that we can add those accounts to a group that will be added to exception.
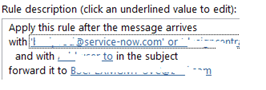
- Block external forwarding set thru outlook rules.
- Block external forwarding set by exchange admins using exchange console or shell.
To get report for outlook forwarding rules, here is the small script for outlook rules created by one of my colleague.
###############################################################
$mailboxes = Get-Mailbox -ResultSize Unlimited
foreach ($mailbox in $mailboxes) {
$forwardingRules = $null
Write-Host “Checking rules for $($mailbox.Name)” -foregroundColor Green
$rules = get-inboxrule -Mailbox $mailbox.identity
$forwardingRules = $rules | Where-Object {$_.forwardto -or $_.forwardasattachmentto -or $_.RedirectTo}
foreach ($rule in $forwardingRules) {
$recipients = @()
$recipients = $rule.ForwardTo | Where-Object {$_ -match “SMTP”}
$recipients += $rule.ForwardAsAttachmentTo | Where-Object {$_ -match “SMTP”}
$recipients += $rule.RedirectTo | Where-Object {$_ -match “SMTP”}
$externalRecipients = @()
foreach ($recipient in $recipients) {
$email = ($recipient -split “SMTP:”)[1].Trim(“]”)
$domain = ($email -split “@”)[1]
$externalRecipients += $email
}
if ($externalRecipients) {
$extRecString = $externalRecipients -join “, ”
Write-Host “$($rule.Name) forwards to $extRecString” -ForegroundColor Yellow
$ruleHash = $null
$ruleHash = [ordered]@{
PrimarySmtpAddress = $mailbox
DisplayName = (Get-mailbox $mailbox).Displayname
RuleId = $rule.Identity
RuleName = $rule.Name
RuleDescription = $rule.Description
ExternalRecipients = $extRecString
}
$ruleObject = New-Object PSObject -Property $ruleHash
$ruleObject | Export-Csv C:\temp\externalrules.csv -NoTypeInformation -Append
}
}
}
#####################################################################
To get the report for OWA/Admin forwarding:
######################################################################
Get-Mailbox -Filter {ForwardingAddress -ne $null -or ForwardingSmtpAddress -ne $null} | Select Name, PrimarySMTPAddress, Alias, ForwardingAddress, ForwardingsmtpAddress, DeliverToMailboxAndForward | Export-csv C:\Temp\exchnagefwding.csv
######################################################################
Collect these users from the report and add these users to the group.
Now you have two ways to block the forwarding, one way is thru transport rule but unfortunately that will not work for Admin level forwarding and other is Security / compliance Outbound Spam policy.
If you just want to block the outlook rules based forwarding, then you can use the exchange transport rule as below:
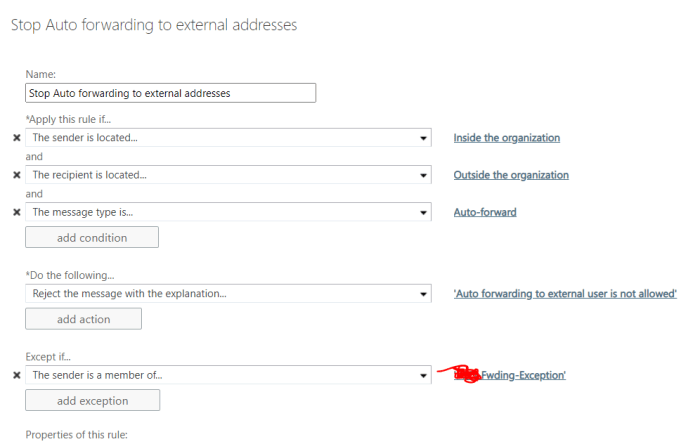
Note: Transport rule will not block forwards done by Admins. Reference:
All you need to know about automatic email forwarding in Exchange Online
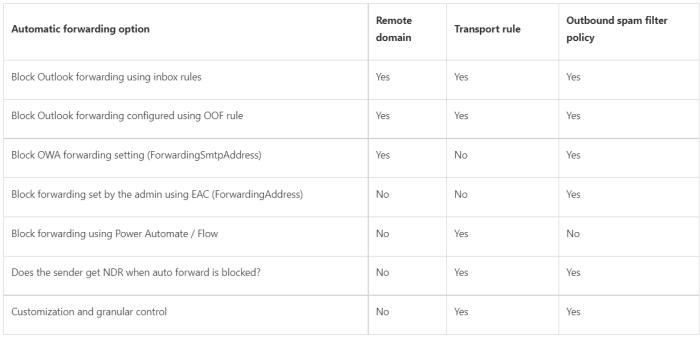
If you want to block all forwarding except set thru powerautomate then use security and compliance policy.
Log on to https://protection.office.com/
à Threat Management à Policy à Create New Policy Outbound
Select the exception group
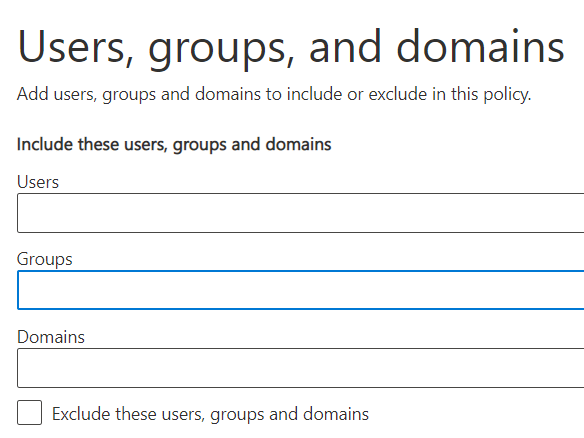
Set the forwarding to ON, rest same settings as default policy.

Now edit the Anti-spam outbound policy (Default)
Set the Forwarding to OFF
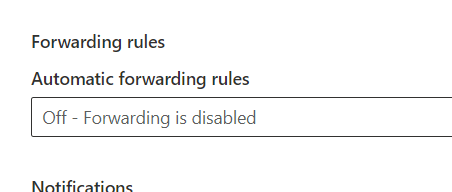
Now forwarding is completely blocked in your environment except for group of users and powerautomate is not covered by this.
If you want to cover powerautomate as well then use transport rule as well as security and compliance method.
You can work on slowly at your own pace to coordinate and remove the accounts from forwarding group except those has business reasons.
Thanks for reading…………
Tech Wizard
Pingback: Block External Email From PowerAutomate | Tech Wizard